Community Finds
If you already have an account, please log in using the button below to post your device. If you don’t have an account yet, please register using the button below and then post your device.

OBD II Tracker Located with Spy Finda V90
Paul Dejesus found a OBD II GPS Tracker with our V90 Spy
Was plugged into my OBDport. Is this a tracker?
Found this in my house!


The Guardian Angel HaloSweep: When “Paranoid” Turns Out to Be True
One of the heaviest burdens of being targeted by digital surveillance isn’t just the invasion of privacy—it’s the isolation.
Recently, we were contacted by a couple in Florida who were at their breaking point. For months, they experienced inexplicable anomalies: their home network would drop, their devices behaved erratically, and private conversations seemed to echo back to them from outside sources. They were embarrassed to even reach out. Friends and family had gently suggested they were imagining things. Local authorities couldn’t do much without physical proof. They felt completely alone and, worse, they were starting to question their own sanity.
They weren’t crazy. They were compromised.
They hired us for a Guardian Angel: HaloSweep. Our team deployed to the undisclosed location in Florida, ready to separate fact from friction. I was on-site as the consulting TSCM Specialist alongside E.M. Investigations, while Tracer—our resident white hat hacker—fired up his equipment to hunt for anomalies in the RF spectrum.
Inside the home, the physical sweeps of the bedrooms and living areas came up clean. No hidden lenses, no hardwired audio bugs. But when Tracer initiated the network analysis, his rig picked up a ghost. A hidden wireless network was broadcasting a powerful signal, aggressively interacting with the home’s legitimate Wi-Fi environment.
Tracer secured his gear and grabbed his Yagi directional antenna, tracking the invisible signal strength out the front door and into the Florida heat. The signal led us away from the walls and right up to the edge of the roof.
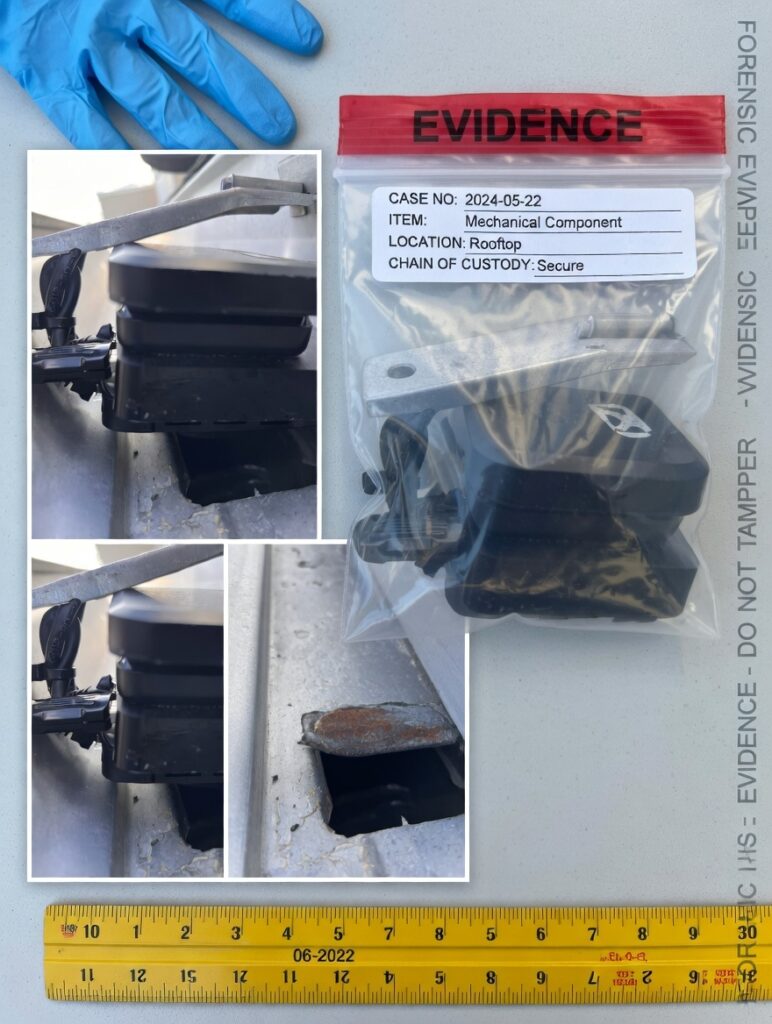
There, wedged perfectly out of sight inside the aluminum rain gutter, was a custom-built rogue access point.
It was a textbook “drop box.” The attacker had daisy-chained heavy-duty battery banks to a T-Mobile cellular hotspot, using it to provide a remote internet backhaul. Plugged directly into the array was a micro-compute stick—the brains of the operation—silently attacking the couple’s network and phoning the stolen data back to the attacker over the cellular connection. By placing it in the gutter, the bad actor bypassed the home’s alarm system entirely while maintaining a perfect line-of-sight signal to the routers inside.
Finding the device was only half the battle; preserving the truth was the other. E.M. Investigations immediately established a perimeter around the drop box. Without disconnecting the power—which could have triggered a dead-man switch to wipe the USB’s memory—they meticulously photographed the rig, documented the MAC addresses, and maintained an unbroken chain of custody until local police arrived to properly bag the hardware as physical evidence.
The couple wasn’t crazy. They had a smoking gun.
While we were able to use the SIM card data and forensic digital footprints to uncover exactly who planted the device, the details of that confrontation must remain completely redacted for now. Catching the bad guy is always refreshing, but the real victory that day was giving that couple their peace of mind, and their home back.


